If your environment does not have a directory service such as Active Directory Domain Services (ADDS), but you still require Microsoft Windows based virtual machines (VMs) in Azure, you can integrate the VM into Entra ID for authentication purposes. This means users can sign-in to a Windows Server VM in Azure using their Entra ID credentials, which provides a number of benefits from a security perspective, including not being reliant on separate independent local user credentials.
To be able to use this functionality, the VM requires the AADLoginForWindows extension to be installed, this can either be installed during VM creation or it can be installed retrospectively. The extension can be installed through the Azure portal, Azure CLI and PowerShell.
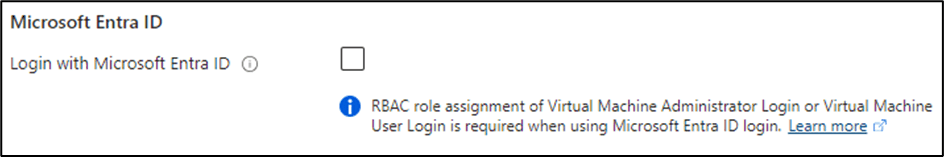
During the VM’s creation in the Azure portal, this extension can be installed during the VM’s deployment process, if the Login with Microsoft Entra ID checkbox is selected:
If the Azure VM already exists, the extension can be installed through the Azure portal manually, using the Extensions + applications blade from the VM’s settings in the Azure portal:
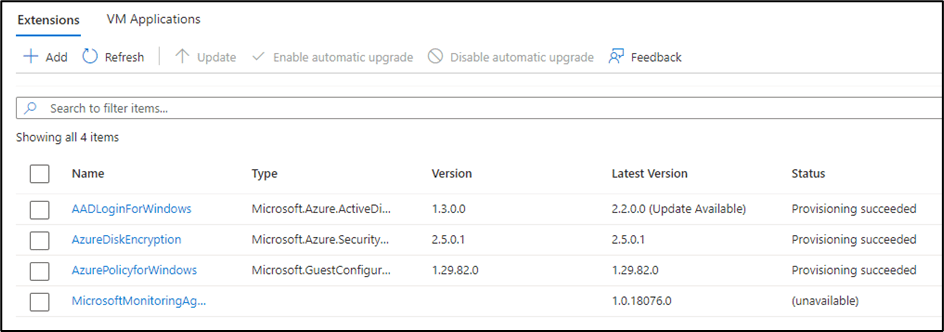
Whichever method you use the AADLoginForWindows extension will show under the Extensions + Applications blade as shown above, and assuming it has installed successfully, the extensions status will show as provisioning succeeded. As shown in the example above, this extension is updated by Microsoft from time to time and does require upgrading, correct at the time of writing this extension does require upgrading manually and does not support the automatic upgrade feature.
Now the extension is installed, all you need to do for this to work is to grant your users the required Azure roles, however the role required depends on what permission levels your user requires. Two Azure roles exist for this purpose Virtual Machine User Login & Virtual Machine Administrator Login. As the names of the roles suggest, the first role provides users accounts with standard user permissions, and the second role provides the user with local administrator permissions.
In a standard environment the above should be all you need to do to allow Entra ID authentication on an Azure VM. However in tenants with more complexity, you may find you need to complete some further troubleshooting and make some additional changes, especially if your tenant is leveraging Microsoft’s conditional access.
If you have a conditional access (CA) policy which enforces MFA, your users will need to authenticate with a strong modern authentication option, such as Windows Hello for Business. If a strong modern authentication option is not possible in your environment, you will need to ensure the conditional access policy which enforces MFA does not do so for this process, this can be done by excluding the Microsoft Azure Windows Virtual Machine Sign-in application in the cloud apps exclusion list in the CA policy.
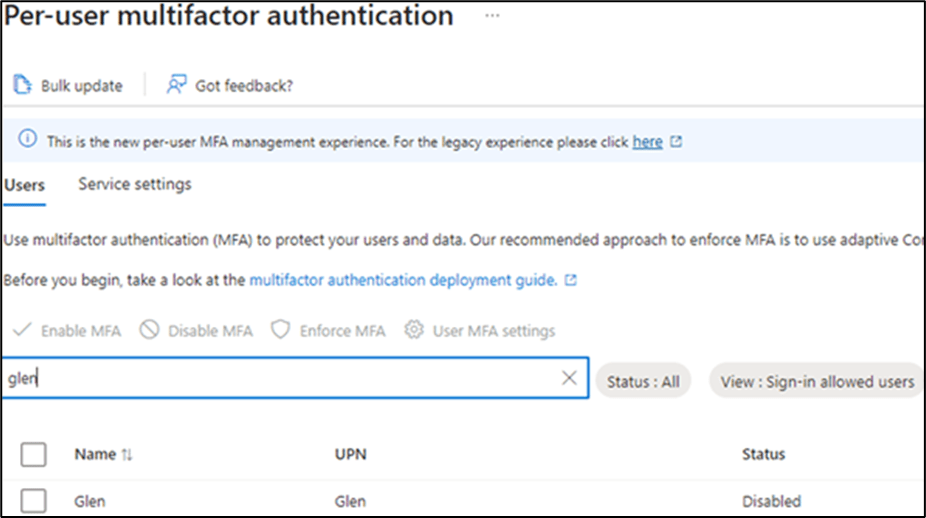
I’ve also found the legacy per-user multifactor authentication settings (if enabled) also interfere with this authentication flow, to resolve this you need to disable this for each user in the Entra ID portal, the settings captured below are available by selecting the Per-User MFA option in the users blade available within the Entra ID portal:
A few other caveats:
- To be able to use modern authentication methods such as Windows Hello for Business, the Use a web account to sign in to the remote computer option, needs to be selected within the RDP client to work successfully:
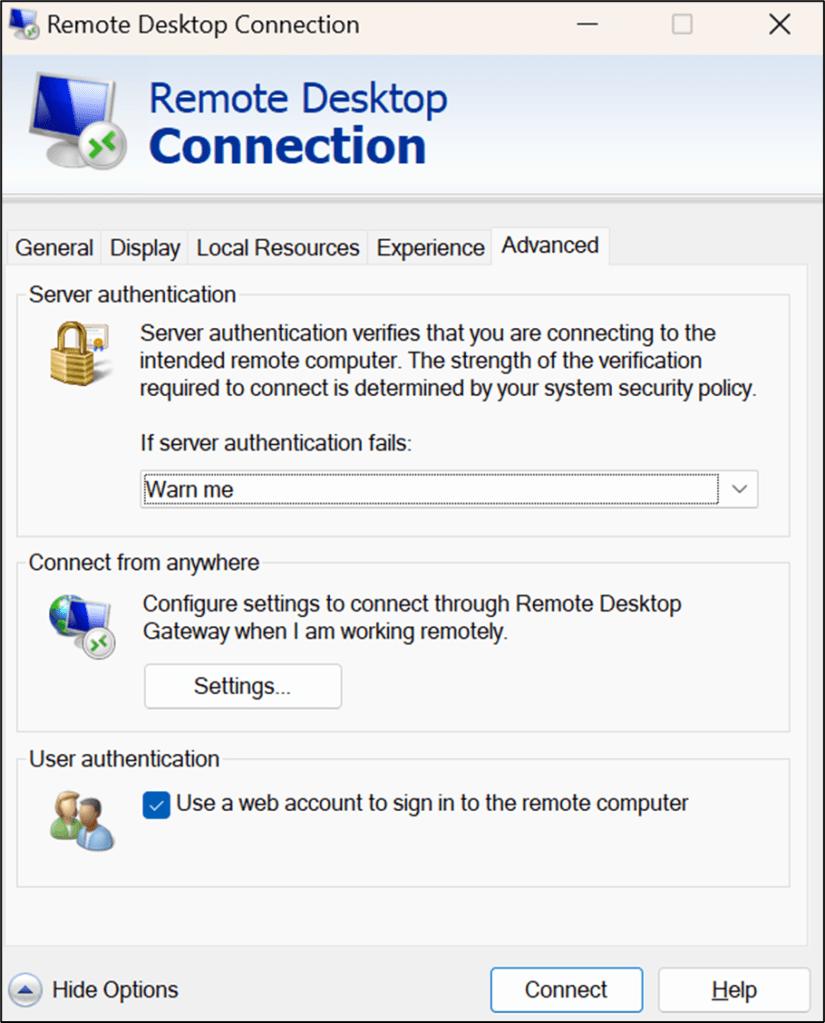
The above setting can of course be saved to an RDP file to ensure this setting does not need to be enabled each time. You can also download a pre-prepared RDP file by using the connect option from the VM’s properties in the Azure portal.
- The device the user is signing in from needs to be either an Entra ID Joined, Entra ID Hybrid Joined or Entra ID registered device. Otherwise, you’ll see sign-in errors at the RDP sign-in prompt, likely to be a generic error saying The logon attempt failed.
- When authenticating from a device which is Entra ID registered, every time a user authenticates with the RDP client they will need to specify the “AzureAD\” prefix, for example “AzureAD\username”.
- This authentication method is unsupported, if you are logging in from another Windows Server, and your tenant has a conditional access policy which enforces access only from compliant devices.
Hope this helps and thanks for reading!