An interesting challenge came my way recently, this was for a global firm with locations in 15 different countries, whilst during an exciting period of growth and aquisition for them.
This article is going to focus on the challenge I faced with regards to the businesses hybrid identity requirements, but first I’d like to provide a bit of background to the project.
The first stage of the project was to merge two seperate firms and all of their offices based in the UK from an IT infrastructure perspective (identity, on-premise servers, cloud resources & networking), both these firms had different specialities however, once merged these two firms would become the firms UK division.
The second stage of the project was to bring the UK division into the global businesses Azure & Entra ID tenant, including users hybrid identities, Intune mobile device management (MDM), Autopilot & Azure IaaS resources.
Due to the nature of the global business, my remit was only in relation to the UK division, divisions located outside of the UK are managed by their own respective IT teams. Therefore, every element delivered as part of this project, could only affect the UK division, whilst allowing other divisions to replicate the behaviour and functionality in the near future.
The challenge: how to use a hybrid identity model for a specific on-premises ADDS forest, with an Entra ID tenant which in the future will require other ADDS forests to also sync, all whilst not having any trusts or connectivity between these multiple ADDS forests.
Over the years the Entra ID Connect (EIDC) sync service installed on a Windows Server, has generally been the go to option for hybrid identity sync between ADDS and Entra ID, however Entra ID has a limitiation whereby it cannot connect to and use multiple Entra ID Connect servers. Which meant this was not a suitable option in this scenario due to the lack of connectivity and trusts between ADDS forests across the globe.
The solution: Entra ID Connect cloud sync.
The primary difference between the Entra ID Connect Cloud Sync service and an on-premises Entra ID Connect server is the sync process is offloaded to the cloud. As the synchronisation process is handled directly within the Entra ID tenant, this method essentially supports multiple forests without the need for line of sight connectivity and trusts between the individual ADDS forests, which suited this scenario perfectly.
To be able to sync multiple forests in this way, a light weight Entra ID Connect Cloud sync agent needs to be installed onto a domain member server within each forest, which is needed to be synced with the Entra ID tenant.
The Entra ID Connect Cloud sync service is more limited when compared to the Entra ID Connect. Although in my opinion the main features are all there, for example the service still allows you to have a two-way sync (AD to Entra ID and Entra ID to AD) including password writeback functionality, as well as OU filtering so you can control which objects are synced. For reference, if you want users to be able to change their ADDS passwords from the cloud, each user will require a Microsoft Entra ID P2 license to be able to change their password via self-service password reset.
The agent installer can be found within the Entra ID portal: login to Entra ID, open the ‘Microsoft Entra Connect’ blade, open the ‘cloud sync blade’, then select ‘New configuration’. Select the ‘AD to Microsoft Entra ID sync’ sync direction, then finally select ‘click here’ next to ‘For a list of active agents,’ this will open a new blade where you can select the option to download the agent installer.
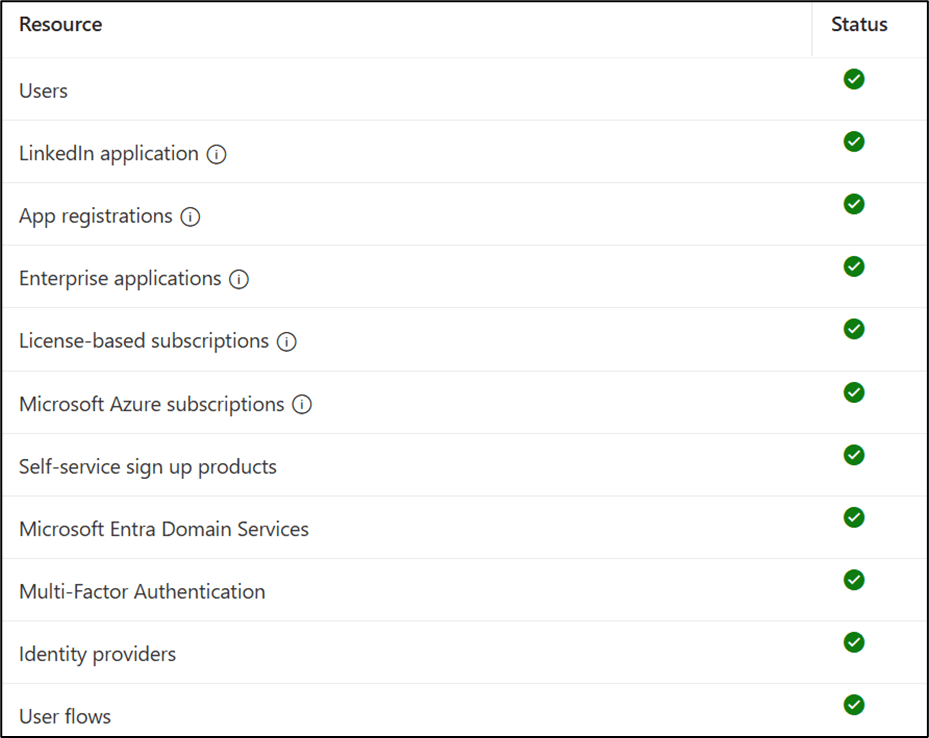
For reference this same blade will also show all provisioning agents registered to the tenant along with their status:
Further information on how to install an Entra ID Connect Cloud Sync agent is available here: https://learn.microsoft.com/en-us/entra/identity/hybrid/install
Hope this helps and thanks for reading!